The Security Reference Your Team Never Opened
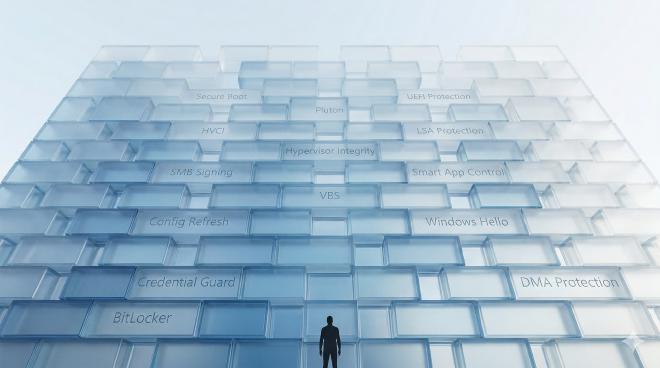
Table of Contents
A CISO’s case for one book across every IT role. #
The most important security tool in your enterprise isn’t a product you bought. It’s a document your team never opened.
One year ago today, a defective content update for CrowdStrike’s Falcon sensor triggered widespread crashes across Windows hosts worldwide. The faulty channel file, timestamped 04:09 UTC on July 19, 2024, caused an out-of-bounds memory read that left affected machines in blue-screen boot loops. Microsoft estimated the incident affected 8.5 million Windows devices – under 1% of all Windows machines – yet the disruption was outsized: airlines grounded flights, hospitals diverted ambulances, and banks across three continents went dark.1
Four months later, Microsoft updated the Windows 11 Security Book for version 24H2 – a free, ~80-page technical reference that walks through every layer of the OS security stack. It covers the kind of kernel-level protections that most IT teams have never inventoried: Hypervisor-Protected Code Integrity that validates kernel code before execution, a Vulnerable Driver Blocklist that prevents known-bad drivers from loading, hardware-enforced stack protection against memory corruption. None of these would have single-handedly prevented the CrowdStrike failure. But the incident exposed a deeper problem: most organizations don’t understand what their own OS is – and isn’t – doing to protect them.
I read it in July. I expected a marketing deck. What I got was the most complete map of Windows endpoint defense I’ve seen – and a realization that the people who need this information the most aren’t reading it.
Microsoft’s free Windows 11 Security Book is the most underread technical reference in enterprise IT today. Here are five REASONS why every IT professional – not just sysadmins – should spend a few hours with it before year-end.
Reason #1: Your Sysadmin Doesn’t Know What’s Already On by Default #
Windows 11 24H2 changed the baseline. Significantly. And most sysadmins are still configuring protections that are now built in.
Config Refresh can auto-revert tampered policy settings every 90 minutes once enabled – even after registry edits or malicious software modifications. SMB now enforces mandatory signing by default, and 24H2 adds the ability to block NTLM for outbound SMB connections. The Windows Firewall CSP applies rules as atomic blocks: all-or-nothing, eliminating the risk of partial deployments leaving security gaps. Account lockout is set to 10 attempts with a 10-minute lockout, admin lockout enabled, out of the box.2
BitLocker’s device encryption prerequisites – DMA and HSTI/Modern Standby – have been removed, making more devices eligible than ever. The preboot recovery screen now hints which Microsoft account holds the recovery key.
Organizations using Windows 11’s default security posture reported a 62% drop in security incidents, including a 3x reduction in firmware attacks.3 That’s not from deploying new tools. That’s from what the OS already does.
The book maps every default. For a sysadmin managing hundreds or thousands of endpoints, that’s the difference between redundant work and informed prioritization.
Reason #2: Your DevOps Team Can’t Secure What They Can’t See #
DevOps teams build, package, and deploy on Windows daily – often without understanding the security primitives available to them.
The book details Win32 App Isolation, a capability that lets developers package desktop applications to run in an AppContainer with least-privilege access. It’s designed to be the default isolation standard for Win32 clients, though parts remain in preview. The Application Capability Profiler lets teams test what their app actually needs in “learn mode” before locking it down – directly relevant to teams packaging software for enterprise deployment.4
Trusted Signing (now Artifact Signing) is Microsoft’s fully managed code signing service – no more wrestling with certificate procurement and renewal. It plugs directly into build pipelines. Windows Sandbox provides a disposable Hyper-V-based desktop for testing untrusted binaries. Everything is wiped on close.
For teams running WSL, the Security Book highlights security capabilities that many developers overlook: Hyper-V Firewall for filtering WSL container traffic, DNS Tunneling for virtualization-aware name resolution, and auto-proxy inheritance from Windows. Microsoft Defender for Endpoint now integrates with WSL distros via a dedicated plug-in. The Linux development environments that were invisible to your security stack no longer have to be.5
Two separate developments signal where memory-safe systems programming is heading: Microsoft has begun introducing Rust into the Windows kernel, and the Pluton security processor’s firmware is built on the open-source Tock OS, a Rust-based platform. Different initiatives, same direction.6
If your DevOps team hasn’t read the Application Security chapter, they’re missing tools that eliminate entire categories of build and deployment risk.
Reason #3: Your Security Specialist Is Missing the Architecture Underneath #
Most security professionals know the feature names – Credential Guard, BitLocker, Defender. Few understand the architectural model that makes them work.
The book explains Virtualization-Based Security (VBS) and its trust level model: VTL0 (the normal OS kernel) and VTL1 (a secure kernel isolated by the hypervisor). Even if VTL0 is fully compromised, secrets stored in VTL1 remain protected. Credential Guard, LSA protection, and VBS key protection all depend on this architecture.7
Dynamic Root of Trust for Measurement (DRTM) goes further. On Secured-core PCs, System Guard Secure Launch forces the CPU into a hardware-controlled trusted state before the OS boots. If a firmware rootkit bypasses UEFI Secure Boot and sits in memory, DRTM prevents it from accessing VBS-protected secrets. Firmware Attack Surface Reduction (FASR) complements this on supported devices where hardware DRTM is unavailable.
Microsoft Pluton integrates the security processor directly into the CPU die – eliminating the physical bus between a discrete TPM and the processor that attackers can intercept. Its firmware is updated through Windows Update.8
Token protection cryptographically binds Microsoft Entra ID tokens to the device. Stolen tokens are useless on another machine. Combined with Conditional Access, this is one of the strongest anti-lateral-movement controls available today.
The architecture chapters are the book’s real contribution. They explain why the protections work, not just what they do. That distinction matters for anyone doing threat modeling, purple-teaming, or incident response on Windows environments.
Reason #4: Your Software Engineers Are Reinventing What the OS Already Provides #
Developers building on Windows routinely implement custom solutions for problems the platform has already solved.
The Cryptography Next Generation API (CNG), powered by Microsoft’s open-source SymCrypt library, provides AES 128/256, RSA up to 4096-bit, ECDSA over P-256/P-384/P-521, SHA-256/384/512, and HKDF – all FIPS 140 validated, with hardware acceleration where available. DPAPI and DPAPI-NG handle static data protection and secure secret sharing between processes.9
Personal Data Encryption offers public APIs for file-level encryption gated by Windows Hello authentication. New in 24H2: this extends automatically to Documents, Pictures, and Desktop folders. VBS Enclaves provide software-based trusted execution environments inside a host application, protecting secrets even from admin-level attackers – available on x64 and ARM64.
Windows 11 is a FIDO2-certified authenticator. Passkey support is native, with a third-party provider plug-in model coming. If your engineers are building authentication flows, passkeys on Windows should be in the design spec now, not later.10
The book catalogs cryptographic primitives, isolation models, and authentication APIs that most developers don’t know exist at the OS level. Every custom implementation of something the platform already provides is a potential vulnerability.
Reason #5: Your CIO Is Approving Budgets Without the Full Picture #
The Windows 11 Security Book contains the business case data that most CIOs never see because it’s buried in a technical reference they assume isn’t for them.
The reported numbers: 62% fewer security incidents. 3x reduction in firmware attacks. 2.9x fewer identity theft instances. A 25% productivity improvement for IT and security teams using chip-to-cloud security. Behind these metrics sits the Secure Future Initiative – 34,000 full-time engineer equivalents dedicated to security, synthesizing 65 trillion signals daily.3
But the strategic sections matter more than the stats. The book lays out how Windows 11 + Microsoft Entra ID + Intune forms the foundation for a Zero Trust security model – device health attestation, Conditional Access, and passwordless authentication working as an integrated system. Administrator protection (currently in preview) introduces just-in-time rights – users run without standing admin privileges; elevation requires per-action approval via Windows Hello. Microsoft Entra Private Access positions identity-centric access as the successor to traditional VPNs – the direction enterprise network security is heading.11
With Windows 10 support reaching end of life on October 14, 2025, the migration conversation is happening now in every organization.12 The CIO who reads this book will ask better questions, challenge vendor pitches more effectively, and understand what they’re actually getting – and leaving on the table – with Windows 11.
The Bottom Line #
- Windows 11’s security defaults changed substantially in 24H2 – most IT teams haven’t caught up
- The book covers seven security layers from silicon to cloud, plus privacy and cloud services
- Five IT profiles – sysadmin, DevOps, security specialist, software engineer, and CIO – each have chapters that challenge their assumptions
- Cloud architects, compliance officers, and IT trainers will also find directly relevant material
- The CrowdStrike incident demonstrated what happens when teams don’t understand kernel-level protections available on their own platform
- It’s free, it’s ~80 pages, and it’s the most efficient way to close the gap between what Windows does and what your teams think it does
The organizations that recover fastest from the next incident won’t be the ones with the biggest security budgets. They’ll be the ones whose people – across every IT function – actually understood what their own platform was doing for them before the crisis hit.
When was the last time your entire IT leadership team read the same security reference – and discussed what it means for how they work?
Read the book: Windows 11 Security Book – free on Microsoft Learn.
CISA, “Widespread IT Outage Due to CrowdStrike Update,” July 19, 2024; Microsoft estimate of 8.5 million affected devices, July 20, 2024; CrowdStrike, “External Technical Root Cause Analysis – Channel File 291,” August 6, 2024. ↩︎
Microsoft, Windows 11 Security Book, Operating System Security: Config Refresh, Firewall CSP, Account Lockout Policies, updated November 2024. ↩︎
Microsoft, Windows 11 Security Book, Security Priorities and Benefits, updated November 2024. ↩︎ ↩︎
Microsoft, Windows 11 Security Book, Application Isolation: Win32 App Isolation and Application Capability Profiler, updated November 2024; Microsoft Learn, “Win32 App Isolation Overview.” ↩︎
Microsoft, Windows 11 Security Book, Application Isolation: Windows Subsystem for Linux, updated November 2024; Microsoft Learn, “Hyper-V Firewall”; Microsoft Learn, “Microsoft Defender for Endpoint Plug-in for WSL.” ↩︎
Microsoft, “What’s New in Windows 11, Version 24H2,” Microsoft Learn (Rust-based GDI region implementation in win32kbase_rs.sys); Microsoft, Windows 11 Security Book, Hardware Security: Microsoft Pluton Security Processor, updated November 2024 (Tock OS as Rust-based firmware foundation). ↩︎
Microsoft, Windows 11 Security Book, Silicon Assisted Security: Virtualization-Based Security, updated November 2024. ↩︎
Microsoft, Windows 11 Security Book, Hardware Security: Microsoft Pluton Security Processor, updated November 2024. ↩︎
Microsoft, Windows 11 Security Book, System Security: Cryptography, updated November 2024; NIST Cryptographic Module Validation Program, Windows CNG module certificates. ↩︎
Microsoft, Windows 11 Security Book, Identity Protection: Passkeys, updated November 2024; FIDO Alliance, Windows Hello FIDO2 certification. ↩︎
Microsoft, Windows 11 Security Book, Cloud Services, updated November 2024. ↩︎
Microsoft, “Windows 10 End of Support,” Microsoft Support lifecycle page; support ends October 14, 2025. ↩︎